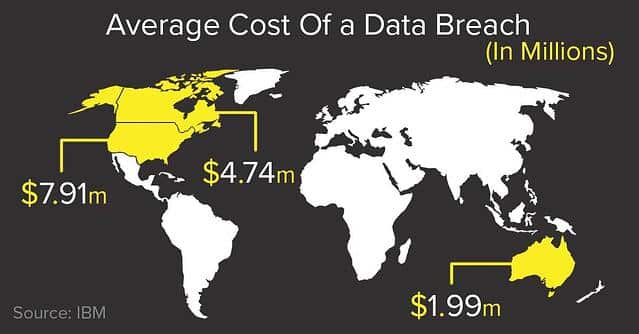
October is National Cybersecurity Awareness Month, and cybersecurity is arguably the hottest topic around technology. IT teams fight a daily battle to keep their company, employee, and client data safe from compromise. Organizations of every size are at risk for an attack, but small/midmarket businesses are particularly targeted, as they generally have less sophisticated security infrastructure and practices, as well as fewer IT personnel to manage and respond to threats. Unfortunately, these organizations are also least likely to survive the cost in dollars, downtime, and reputation of a cyberattack. These, and many more facts surrounding today’s security environment for small/midmarket businesses are highlighted in Cisco’s Cybersecurity Special Report. As a Cisco partner with extensive experience in this sector, Liberty Technology’s CEO Ben Johnson contributed valuable insight to the study.
As part of our efforts to help organizations fight the fine fight, Liberty is encouraging organizations to reinforce their cybersecurity by gaining insight into your organization’s presence on the dark web.
The dark web is a sublayer of the Internet that is hidden from conventional search engines like Google, BING, and Yahoo. These are able to access only .04 percent of the “surface” Internet. The remaining 99.96 percent of the Internet consists of databases, private academic and government networks, and the Dark Web. Because you can operate anonymously, the dark web holds a wealth of stolen data and illegal activity.
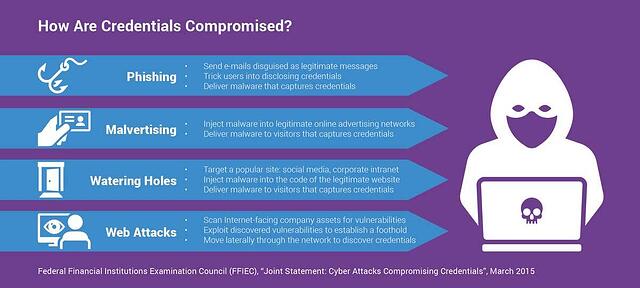
The result is a constant interplay of new threats and new methods to detect and combat them. But cybercriminals are relentless. Even two-factor authentication can easily be hacked by intercepting codes or exploiting account recovery systems – particularly via mobile. If an employee uses a business email address to create an account on another service, usually with the same or similar password, and that service gets breached, those credentials can be used to hack the employer’s network.
Likewise, encrypted data is only as safe as the encryption key. Once that is published, much of that data is no longer safe. The LinkedIn breach is a great example of this.
Liberty offers credentials monitoring as a powerful tool to combat these threats. Our dark web scanning supports your own internal IT department by providing them an early warning system to help mitigate the effects caused by a breach. It provides them with a service they’re unable to access on their own in helping them protect your organization.
Dark Web ID is designed to help both public and private sector organizations detect and mitigate cyberthreats that leverage stolen email addresses and passwords. With a combination of human and artificial intelligence, the service scours hundreds of thousands of dark web sites each day.
Take an important step in supporting your IT security and contact us to learn more and to request your unique Dark Web ID report. Liberty will be here to help you in case of any breach-related damage, but knowing about it early or preventing it altogether is always the better course of action to keep your organization safely and seamlessly doing what you do best.
To request this report all you need to do is send an email to sales@libertytech.net with your domain and permission to pull the report. Or request a more in depth security assessment HERE.